Securing cryptocurrency can feel daunting, especially when the stakes involve real money and digital assets. For anyone venturing into Ethereum, whether for investment, decentralised finance (DeFi), or collecting NFTs, setting up a secure wallet is the essential first step. An Ethereum wallet is more than just a place to store tokens: it’s the gateway to interacting with the blockchain, managing private keys, and safeguarding one’s financial sovereignty. Yet with phishing attacks, scams, and hacking incidents making headlines, understanding how to set up and protect a wallet properly has never been more critical. This guide walks through the types of Ethereum wallets available, how to choose the right one, and the step-by-step process to set up and secure it, empowering users to take control of their crypto journey with confidence.
Key Takeaways
- Setting up an Ethereum wallet is the essential first step for securing cryptocurrency, managing private keys, and interacting with the blockchain safely.
- Hot wallets offer convenience for frequent transactions but are more vulnerable to hacking, whilst cold wallets provide superior security by keeping private keys offline.
- Non-custodial wallets grant full control over your Ethereum and private keys, aligning with decentralisation principles, but require careful management of recovery phrases.
- Always write down your recovery phrase by hand and store it securely offline—never share it or store it digitally, as it’s the master key to your wallet.
- Recognising phishing scams, verifying website authenticity, and enabling two-factor authentication are critical practices for protecting your Ethereum wallet long-term.
- A hybrid approach—using a hot wallet for daily transactions and a hardware wallet for substantial holdings—balances convenience with robust security.
Understanding Ethereum Wallets: Types and Key Differences
Before diving into setup, it’s important to grasp what an Ethereum wallet actually does. Contrary to popular belief, wallets don’t store cryptocurrency itself, they store the private keys that grant access to Ethereum on the blockchain. The type of wallet chosen determines how these keys are stored, managed, and protected.
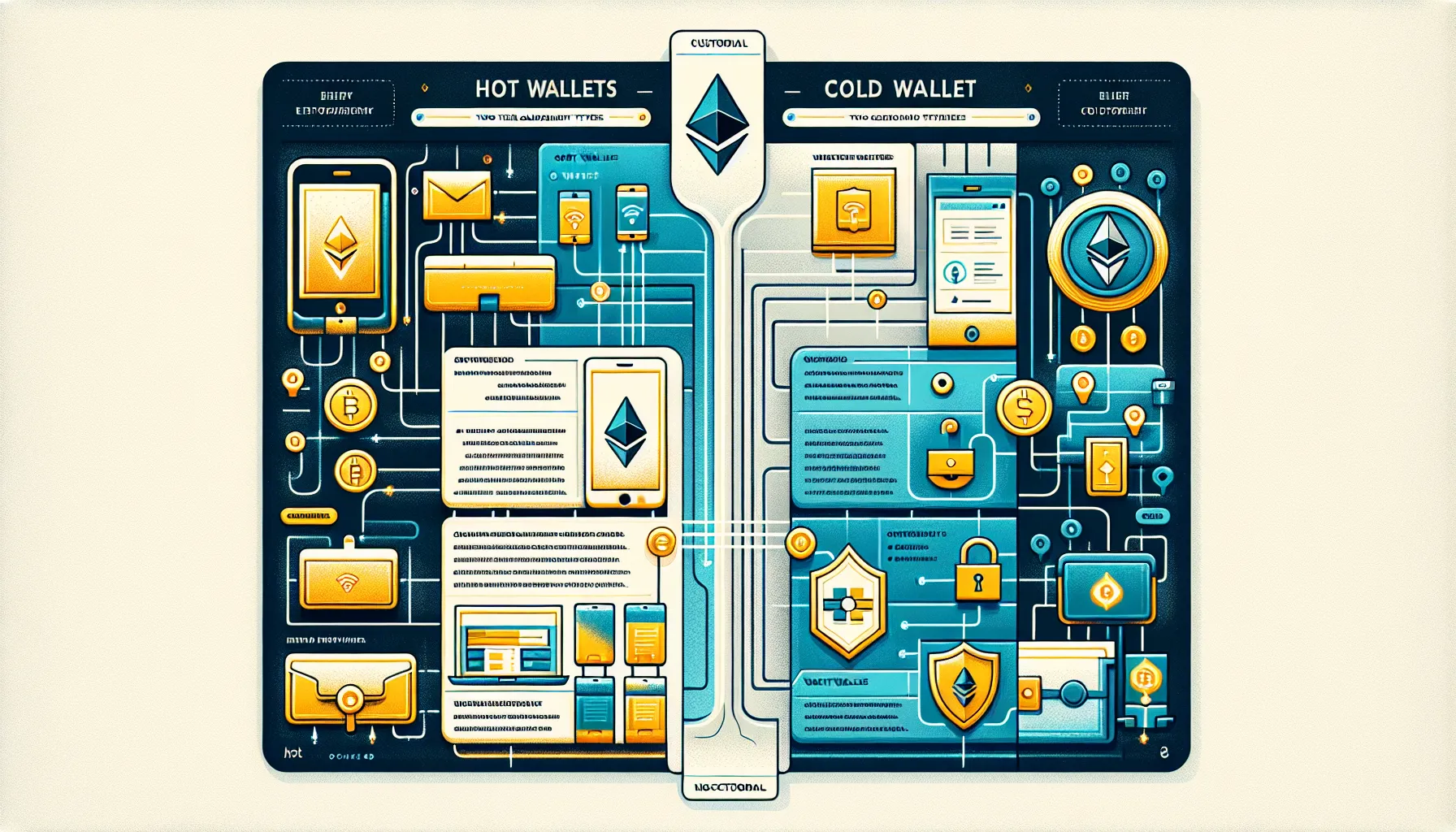
Hot Wallets vs Cold Wallets
The fundamental divide in Ethereum wallets is between hot and cold storage.
Hot wallets are always connected to the internet. They include software wallets, browser extensions, mobile apps, or web-based platforms, that provide quick and convenient access to funds. Popular examples include MetaMask, Trust Wallet, and Coinbase Wallet. Hot wallets excel at ease of use, making them ideal for frequent transactions, interacting with DeFi protocols, or trading NFTs. But, their constant online presence also exposes them to a broader attack surface. Hackers target hot wallets through malware, phishing, and compromised devices, which makes them inherently more vulnerable than their offline counterparts.
Cold wallets, by contrast, keep private keys completely offline. These typically take the form of hardware devices, such as the Ledger Nano X or Trezor Model T, or even paper wallets (though the latter are less common now). Because cold wallets are disconnected from the internet, they’re virtually immune to remote hacking attempts. They’re best suited for long-term storage of substantial holdings, where security trumps convenience. The trade-off is accessibility: users must physically connect the device or retrieve the paper to sign transactions, which can be cumbersome for day-to-day use.
Custodial vs Non-Custodial Options
Another critical distinction lies in who controls the private keys.
Custodial wallets are managed by a third party, typically an exchange or service provider. The company holds the user’s private keys on their behalf, handling security and recovery. This arrangement offers convenience: users can reset passwords, get support, and often enjoy a user-friendly interface. But, it also means relinquishing control. If the provider is hacked, goes bankrupt, or freezes accounts, users may lose access to their funds. Custodial wallets represent a trust-based model, where security depends on the provider’s infrastructure.
Non-custodial wallets put full control, and full responsibility, in the user’s hands. Only the wallet owner possesses the private keys and recovery phrase. There’s no intermediary to call if keys are lost, but there’s also no counterparty risk. Non-custodial wallets align with the ethos of decentralisation and self-sovereignty that underpins Ethereum and the broader crypto movement. Examples include MetaMask (when used as a browser extension) and hardware wallets like Ledger.
Choosing between custodial and non-custodial hinges on one’s comfort with responsibility and technical confidence. Beginners often start with custodial options for ease, then migrate to non-custodial wallets as they gain experience and understanding.
Choosing the Right Ethereum Wallet for Your Needs
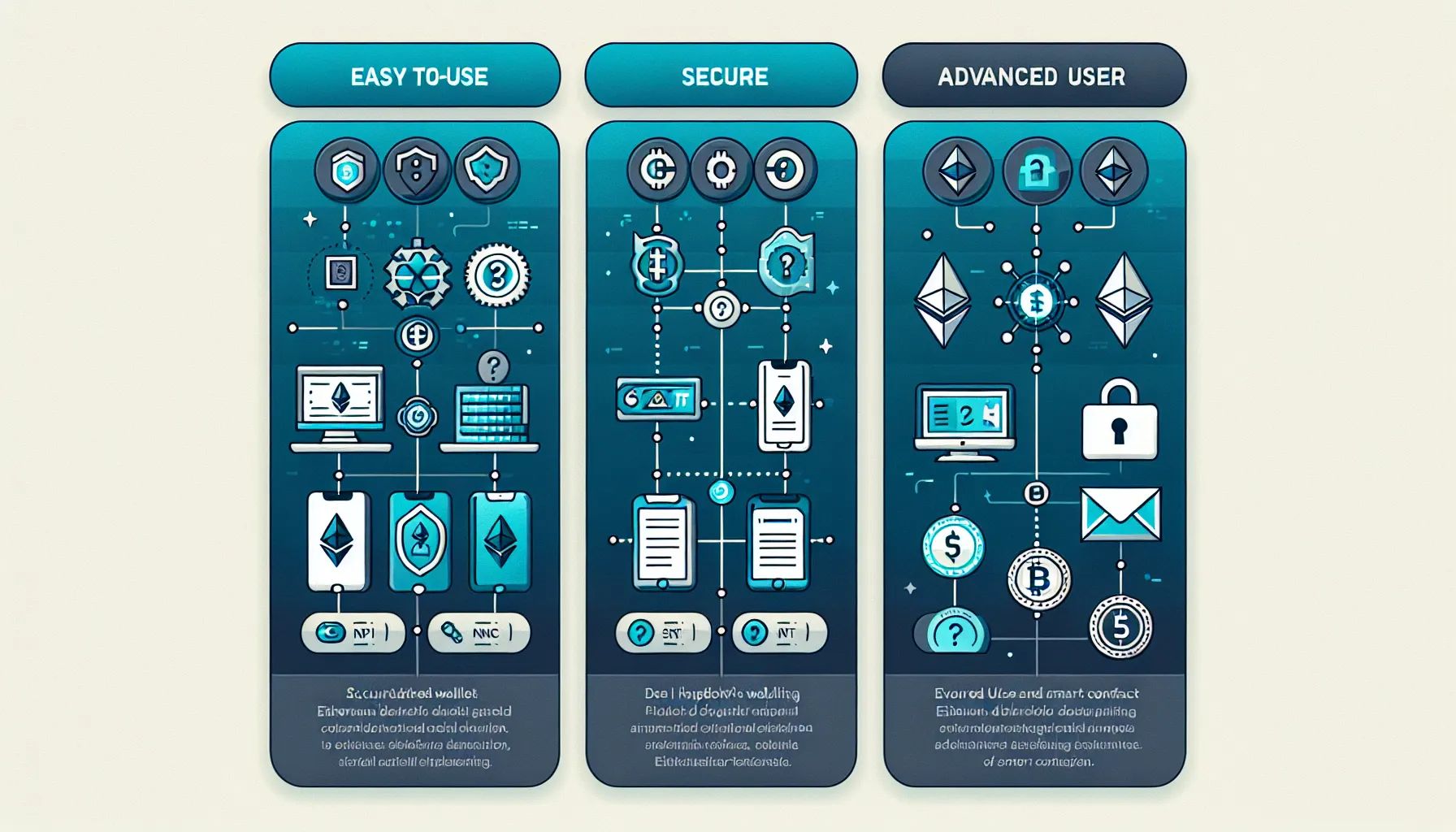
Selecting an Ethereum wallet isn’t a one-size-fits-all decision. The right choice depends on how often transactions are made, the amount being stored, and the user’s technical comfort level.
For beginners dipping their toes into Ethereum, simplicity and support matter most. Custodial wallets or straightforward non-custodial hot wallets like eToro Money Wallet or MetaMask are popular starting points. These platforms offer intuitive interfaces, onboarding tutorials, and, in the case of custodial options, customer support to guide new users. MetaMask, in particular, strikes a balance: it’s non-custodial (so users control their keys) but user-friendly enough for first-timers. It also integrates seamlessly with countless Ethereum-based applications, making it a versatile choice.
For security-focused users or those holding significant amounts of Ethereum, hardware wallets are the gold standard. Devices like the Ledger Nano X and Trezor Model T provide robust offline storage, protecting assets from online threats. They’re particularly recommended for long-term holders who don’t need constant access to their funds. The upfront cost of a hardware wallet (typically between £50 and £150) is a small price for the peace of mind and security it delivers.
Those engaged in DeFi, staking, or NFT trading need wallets that offer both security and flexibility. MetaMask and Trust Wallet are top contenders here. They support a wide range of tokens and decentralised applications (dApps), allow custom network configurations, and provide mobile and desktop access. Their non-custodial nature means users retain full control, essential when interacting with smart contracts and protocols where trust is minimised.
Eventually, many experienced users adopt a hybrid approach: a hot wallet for everyday transactions and a cold wallet for long-term savings. This strategy balances convenience with security, ensuring that the bulk of one’s holdings remain safe whilst keeping a smaller, accessible amount for active use.
Step-by-Step Guide to Setting Up Your Ethereum Wallet
Setting up an Ethereum wallet is straightforward, but attention to detail is crucial, especially when it comes to backing up recovery information.
Creating a Software Wallet
- Choose a reputable wallet: Start by selecting a trusted software wallet. MetaMask and Trust Wallet are widely used and well-reviewed options. Research the wallet’s reputation, user reviews, and security track record before committing.
- Download from the official source: Always obtain the wallet directly from the official website or verified app store listing. Phishing sites and fake apps are common traps. For MetaMask, that means visiting metamask.io or downloading from the Chrome Web Store, Apple App Store, or Google Play. Never download from third-party links or unsolicited emails.
- Follow the setup prompts: Once installed, open the wallet and select the option to create a new wallet. The software will guide the user through the process. This typically includes agreeing to terms of service and setting up a password. Choose a strong, unique password, something unrelated to other accounts.
- Securely note your recovery phrase: The wallet will generate a recovery phrase (also called a seed phrase), usually 12 or 24 words. This phrase is the master key to the wallet. Write it down by hand on paper, never store it digitally, screenshot it, or email it to yourself. The wallet will often ask the user to confirm the phrase by selecting words in order, ensuring it’s been recorded correctly.
- Never share your recovery phrase: This cannot be overstated. Anyone with access to the recovery phrase can control the wallet and drain its funds. Legitimate support teams will never ask for it.
Setting Up a Hardware Wallet
- Purchase directly from the manufacturer: To avoid tampering, buy hardware wallets only from the official manufacturer’s website or authorised retailers. Second-hand devices or those from unofficial sources may be compromised.
- Connect the device and initialise: Plug the hardware wallet into a computer or mobile device using the provided cable. Download the official companion software (Ledger Live for Ledger devices, Trezor Suite for Trezor). Follow the on-screen instructions to initialise the device.
- Write down the recovery phrase: During setup, the device will display a recovery phrase on its screen. Write this down carefully, in order, on the recovery card provided. Store this card in a secure, offline location, such as a safe or lockbox. Some users create multiple copies and store them in different physical locations for redundancy.
- Set a strong PIN: The device will prompt the user to create a PIN code. Choose something memorable but not easily guessed. This PIN is required each time the device is connected, adding a layer of physical security.
Backing Up Your Recovery Phrase Safely
The recovery phrase is the single most important element of wallet security. If a device is lost, stolen, or damaged, the recovery phrase is the only way to restore access.
- Write it by hand: Resist the temptation to store the phrase digitally. Handwriting on paper keeps it offline and immune to hacking.
- Store it securely: Place the written phrase in a safe, lockbox, or bank deposit box. Some users opt for fireproof and waterproof safes. Consider the physical risks, theft, fire, flood, and plan accordingly.
- Never enter it on websites or apps: Scammers often create fake wallet interfaces that prompt users to “verify” or “restore” their wallet by entering the seed phrase. This is always a scam. The recovery phrase should only be entered into the original wallet software during a legitimate recovery process on a trusted device.
- Consider redundancy: For high-value holdings, creating a second backup stored in a separate location adds resilience. Some advanced users even explore metal backups (engraved or stamped recovery phrases) for added durability.
Essential Security Practices for Ethereum Wallets
Creating a wallet is just the beginning. Maintaining its security requires ongoing vigilance and adherence to best practices.
Protecting Your Private Keys and Seed Phrases
Private keys and seed phrases are the crown jewels of cryptocurrency security. Compromising them means losing everything.
- Never share them: No legitimate service, support team, or developer will ever ask for private keys or seed phrases. Anyone making such a request is attempting to steal funds.
- Avoid digital storage: Storing seed phrases in plain text files, cloud storage, password managers, or even encrypted files on internet-connected devices introduces risk. Offline, physical storage is the safest approach.
- Be wary of screen sharing: When seeking technical support, never share screens that might expose sensitive information. Scammers pose as support agents and request remote access or screen shares to harvest keys.
Enabling Two-Factor Authentication and Additional Security Layers
Whilst not all wallets support two-factor authentication (2FA) due to their decentralised nature, those that do, especially custodial and some software wallets, should have it enabled immediately.
- Use strong, unique passwords: Every wallet should have its own password, distinct from other accounts. Password managers (stored offline or using reputable encrypted services) can help manage complexity.
- Set PINs and biometric locks: For hardware wallets and mobile software wallets, utilise PINs, fingerprint recognition, or face ID. These add friction for anyone attempting unauthorised access.
- Keep software updated: Wallet developers regularly release updates to patch vulnerabilities and improve security. Enable automatic updates where possible, or check for updates manually on a regular schedule.
- Verify wallet addresses carefully: Before sending Ethereum, double-check the recipient’s address. Malware can intercept clipboard data and replace copied addresses with an attacker’s. Verifying the first and last few characters is a good habit, but checking the entire address is even better.
Recognising and Avoiding Common Ethereum Scams
The Ethereum ecosystem, like much of the crypto world, attracts opportunistic scammers. Awareness is the first line of defence.
- Ignore unsolicited messages: Whether via email, social media, or messaging apps, unsolicited contact asking for keys, seed phrases, or offering “help” is almost always malicious. Legitimate projects and support teams don’t reach out uninvited.
- Confirm website authenticity: Phishing sites mimic popular wallets, exchanges, and DeFi platforms. Always type URLs directly into the browser or use trusted bookmarks. Look for HTTPS and verify the domain spelling carefully.
- Distrust promises of guaranteed returns: Offers that sound too good to be true, such as “double your ETH” giveaways or unrealistic staking rewards, are scams. Ethereum’s ecosystem involves risk, and no legitimate project guarantees returns.
- Be cautious with smart contracts: When interacting with DeFi protocols or NFT marketplaces, understand what permissions are being granted. Some malicious contracts request unlimited access to wallet funds. Use tools like Etherscan to review contract details before approving transactions.
- Watch out for fake support: Scammers often impersonate official support accounts on social media, responding to user complaints with “helpful” links or requests for personal information. Always verify authenticity through official channels.
Best Practices for Long-Term Wallet Management
Securing an Ethereum wallet isn’t a one-time task. Long-term success requires ongoing diligence and periodic reviews.
Use cold storage for substantial holdings: If Ethereum holdings grow beyond what one can afford to lose, moving the majority to a hardware wallet is wise. Hot wallets are convenient, but they’re also targets. Keeping only a small, manageable amount in a hot wallet for transactions reduces exposure.
Make redundant, offline backups: Recovery phrases should have multiple backups stored in different secure locations. This guards against loss from fire, theft, or natural disaster. Some users split backups geographically, one at home, one in a bank deposit box, for example.
Periodically review security strategies: As technology and threats evolve, so should security practices. Every six months or so, revisit wallet setups, update software, rotate passwords if necessary, and reassess storage locations. Stay informed about new scams and vulnerabilities reported in the Ethereum community.
Test recovery processes: It’s worth testing the wallet recovery process with a small amount of funds before relying on it in an emergency. This ensures the recovery phrase has been recorded correctly and that the user understands the restoration process.
Consider estate planning: Cryptocurrency poses unique challenges for inheritance. If significant assets are held in a wallet, consider how loved ones will access them if something happens. This might involve securely sharing recovery information with a trusted person or using a legal solution like a crypto-aware estate planner.
Stay educated: The Ethereum ecosystem moves quickly. Following reputable news sources, community forums, and official project channels helps users stay aware of emerging threats, new security tools, and best practices. Knowledge is one of the most effective defences against loss.
Conclusion
Setting up an Ethereum wallet and keeping it secure is a foundational skill for anyone engaging with blockchain technology. By understanding the differences between hot and cold wallets, custodial and non-custodial options, users can choose the right tool for their needs. Following careful setup procedures, especially when backing up recovery phrases, ensures that access to funds is preserved. Adopting robust security practices, from protecting private keys to recognising scams, guards against the myriad threats in the crypto landscape. And maintaining vigilance over time, with regular reviews and updates, keeps wallets resilient as the ecosystem evolves. With these steps and precautions in place, users can confidently navigate the Ethereum network, knowing their assets are as secure as their diligence allows.
Frequently Asked Questions
What is the difference between a hot wallet and a cold wallet for Ethereum?
Hot wallets are connected to the internet, offering convenient access for frequent transactions, DeFi, and NFT trading. Cold wallets store private keys completely offline, typically as hardware devices, providing superior security for long-term holdings but less accessibility.
How do I safely store my Ethereum wallet recovery phrase?
Write your recovery phrase by hand on paper and store it in a secure, offline location such as a safe, lockbox, or bank deposit box. Never store it digitally, screenshot it, or share it with anyone, as it’s the master key to your funds.
Should I use a custodial or non-custodial Ethereum wallet?
Custodial wallets offer convenience and support but require trusting a third party with your private keys. Non-custodial wallets give you full control and align with decentralisation principles, though you bear complete responsibility for security and cannot recover lost keys through support.
Can I recover my Ethereum wallet if I lose my device?
Yes, if you have securely stored your recovery phrase (seed phrase), you can restore your Ethereum wallet on any compatible device. Without this phrase, recovery is impossible, which is why backing it up safely is essential.
What is the best Ethereum wallet for beginners in 2025?
MetaMask is highly recommended for beginners due to its user-friendly interface, non-custodial control, and seamless integration with Ethereum applications. Alternatively, custodial options like Coinbase Wallet offer simplicity with customer support for those prioritising ease of use.
How can I protect my Ethereum wallet from phishing scams?
Always download wallets from official sources, verify website URLs carefully, never share your private keys or recovery phrase, and ignore unsolicited messages offering help. Use bookmarks for trusted sites and double-check recipient addresses before sending transactions.